Information Security Risk Management
Information and Communications Security Risk Management Framework
- The Company’s Audit Office serves as the supervisory unit for information security. It is responsible for auditing the implementation status of information security, proposing relevant improvement plans, and conducting regular follow-ups in order to reduce information security risks.
- On November 18, Year 114, the Company’s Board of Directors approved the appointment of the Head of Information Security. Going forward, the Company will report the implementation status of information security to the Board of Directors on a periodic basis as needed.
Information Security Policy
Established in December, Year 113
I. Purpose
To ensure the sustainable operation of the Company’s information services, strengthen information
and communications security management, and establish a secure and reliable digital environment,
thereby ensuring the security of computer data, information systems, information equipment, and
network equipment.
II. Scope
This policy applies to the Company’s administrative-use personal computers (non-testing use,
non-fixture/jig equipment use), and all personal computers directly connected to the network such as
information systems and file-sharing systems, as well as servers and network equipment, and all
employees who use the above equipment and systems.
III. Information Security Policy
In order to achieve the Company’s information security objectives, this Information Security Policy
is established and shall be implemented by the information unit. The Company shall conduct a
self-assessment once each year to reflect the latest developments in the Company’s current status,
information technology, and business operations, and to ensure the effectiveness of information
security practices. To implement information security management, relevant information security
requirements shall be announced to all employees in written or electronic form for joint compliance.
1. Scope Covered by Information Security:
(1) Management systems
(2) Operating procedures
(3) Personnel
(4) Software
(5) Application systems
(6) Computer operating systems
(7) Hardware
(8) Network equipment
(9) Handheld/mobile devices
(10) Storage of data, documents, and media, and
(11) Physical facilities, etc.
Scope of Information Security Management:
The Company’s information security management covers nine information security management items to
prevent improper use, leakage, tampering, destruction, etc. caused by human negligence, malicious
intent, or natural disasters, and to reduce the potential risks and impacts to the Company. The
security management items are as follows:
(A) Information security organization.
(B) Personnel security and management.
(C) Asset classification and control.
(D) Physical and environmental security management.
(E) Communications and operations management.
(F) Access control.
(G) System development and maintenance.
(H) Internal audit and others.
A. Information Security Organization
1. Organizational Structure
(1) To centrally plan, evaluate, supervise, coordinate, promote, and manage security matters of the
Company’s overall information services, the Company has established a Computer Center.
(2) The Computer Center is staffed with one functional supervisor and one specialist.
2. Organizational Duties
(1) Plan, execute, and control information security work across the Company; conduct risk
assessments and implement system security control measures.
(2) Supervise information security management items and perform compliance checks with the
Information Security Policy.
(3) Maintain information confidentiality and audit the management of the use of information
equipment and networks.
(4) Conduct risk assessments and strictly control access permissions when information access is
opened to external entities due to business needs.
B. Personnel Security and Management
1. Security for Personnel Work and Resource Allocation
(1) Conduct appropriate information security assessments and adjustments for personnel hiring,
transfers, resignation, or retirement.
(2) Implement appropriate segregation of duties for employees who can access confidential/sensitive
information or systems and those granted special access privileges, to disperse responsibilities and
authority; conduct general education training; and establish personnel and facility backup
mechanisms.
2. User Training and Confidentiality Responsibilities
(1) New hires and current employees shall sign the Company’s confidentiality undertaking to ensure
the fulfillment of confidentiality responsibilities.
(2) Employees must understand the Company’s Information Security Policy.
(3) Provide appropriate information security education and training based on employees’ job
levels.
(4) The Computer Center shall announce information security-related information at any time.
(5) Personnel may be assigned from time to time to participate in external trainings, seminars, and
product exhibitions.
3. Reporting and Handling of Security and Failure Incidents
(1) Establish information security operating procedures and responsibilities for employees
(including requirements for custody and use of equipment and operational guidelines).
(2) Establish authorization levels for handling information security conditions.
C. Asset Classification and Control
1.Information asset inventories shall be provided by each responsible unit, and the completeness of
asset numbering and the inventory shall be ensured. Information assets are classified into seven
categories based on their nature: hardware, software, communications, data, personnel, documents,
and environment. The classification and control are as follows:
(i) Hardware Assets
(1) Computer equipment, e.g., servers, hosts, monitors, laptops, personal computers, printers,
etc.
(2) Communication equipment, e.g., routers, network switches, modems, fax machines, etc.
(3) Storage media, e.g., tapes, tape drives, tape cabinets, optical discs, optical disc drives,
etc.
(4) Other technical equipment, e.g., uninterruptible power supply (UPS) systems and generators for
server rooms, etc.
(ii) Software Assets
(1) Packaged software, e.g., system software, application software, utility software, network
software, etc.
(iii) Communications Assets
(1) Local area networks and communications services.
(iv) Data Assets
(1) System data, e.g., databases, applications, and backup data, etc.
(2) Electronically stored document files, e.g., system/software manuals and training materials,
etc.
(v) Personnel Assets
(1) Includes all employees (classified by grade/position) and security personnel, etc.
(vi) Document Assets
(1) Paper-based management documents, e.g., system documents, manuals, procedures, and management
regulations, etc.
(2) Paper records, e.g., application forms and procurement/maintenance contracts, etc.
(vii) Environmental Assets
(1) Power systems, air-conditioning systems, etc.
2. Information Asset Classification and Labeling
(i) To ensure proper handling of information assets, an information asset register shall be
established, and the confidentiality, integrity, and availability classifications of each
information asset shall be indicated in the register.
(ii) Important physical information assets shall be labeled based on their availability level
(acceptable downtime) or emergency response requirements to facilitate urgent handling.
3. Information Asset Security Controls
(i) Hardware Controls
(1) Information assets restricted to internal personnel may not be accessed by external persons
without authorization.
(2) Sensitive information assets shall be protected by passwords and may be accessed only after
authorization.
(3) Backups shall be made using storage media (e.g., tapes, optical discs, hard drives) and properly
kept. Backup media containing sensitive information shall be stored in locked cabinets.
(4) When disposal is required, non-public information shall be ensured to be non-recoverable.
Storage media such as disks or hard drives shall be formatted or degaussed; physical destruction
shall be adopted when necessary.
(ii) Software Controls
(1) Software use shall comply with copyright requirements.
(2) Software from unknown sources or downloaded from the internet shall be scanned for viruses or
tested in advance.
(iii) Communications Controls
(1) The installation environment shall be considered and appropriate protection shall be
provided.
(2) Electrical safety shall be evaluated, and cables shall be properly protected.
(3) Regular maintenance shall be performed, and testing shall be conducted when necessary.
(iv) Personnel Controls
(1) Personnel shall receive basic information security awareness training and periodic
education.
(2) Backgrounds and competencies of personnel handling sensitive information/business or performing
important duties shall be screened.
(3) When personnel transfer or resign, permissions shall be updated and information assets shall be
handed over.
(v) Data and Document Controls
(1) Paper documents may be viewed and used only by authorized personnel; no viewing or use is
permitted without authorization.
(2) Sensitive paper documents shall be stored in locked cabinets and may be accessed and used only
with authorization.
(3) When disposal is required, non-public documents shall be shredded or burned. Disposal of
sensitive documents shall be supervised by relevant personnel.
(vi) Environmental Controls
(1) The installation environment shall be considered and appropriate protection shall be
provided.
(2) Electrical safety shall be evaluated, and cables shall be properly protected.
(3) Regular maintenance shall be performed, and testing shall be conducted when necessary.
(4) Information shall be cleared upon decommissioning.
IV. Physical and Environmental Security Management
(i) Secure Areas
(1) For computer server rooms and areas with important information equipment, entry/exit personnel
shall be subject to necessary access control by management staff and their activities shall be
supervised.
(2) Establish computer room security management rules (e.g., no smoking or food/drinks).
(3) Confidential hosts/servers must be managed by dedicated personnel.
(4) Non-management personnel entering/leaving controlled areas of confidential hosts/servers shall
complete and sign entry/exit logs for record-keeping and traceability.
(ii) Equipment Security
(1) Equipment maintenance shall be performed by authorized maintenance personnel.
(2) Establish equipment security management rules (e.g., power supply and backup power).
(3) Equipment requiring special protection shall be properly segregated from general equipment.
(4) Implement necessary security control procedures for employees’ personal information devices
(e.g., mobile phones, portable drives).
(5) Placement and arrangement of information equipment shall take safety into consideration.
(6) The placement of information equipment shall be reviewed and evaluated for potential hazards
such as fire, smoke, water, dust, vibration, chemical effects, power supply issues, and
electromagnetic radiation.
(7) Security equipment shall be inspected regularly, and employees shall receive appropriate
training on the use of security equipment.
(8) Install temperature and humidity gauges to confirm normal temperature and HVAC operation in the
server room, thereby ensuring safe operation of information equipment.
(9) The equipment server room shall be checked on working days; daily inspections shall be performed
and signed in the server room log to ensure daily operation and safety.
(iii) General Control Measures
(1) Strict protection measures are established for portable computer equipment (e.g., password
protection, file encryption, dedicated custody) and shall be implemented.
(2) Computers processing sensitive data shall be shut down, logged out, protected with screen
passwords, or safeguarded by other control measures when not in use.
D. Communications and Operations Management
1. Operating Procedures and Responsibilities
(1) Establish secure operating procedures for important information processing equipment.
(2) Establish information security incident reporting procedures and report incidents in accordance
with the requirements.
(3) For important information processing equipment, establish appropriate operating procedures and
management responsibilities.
(4) Establish procedure records for major system changes.
(5) System development and production operations must be separated and handled in different system
environments.
(6) When entering into an information security processing agreement with a vendor, assign relevant
security maintenance responsibilities and incorporate them into the contract terms.
(7) In principle, the duties of information system use, data entry, system operations, network
management, system development and maintenance, change management, and security management shall be
performed by different personnel with segregated responsibilities.
(8) For information services with high security requirements, the responsibilities for information
security management and execution shall be distributed.
(9) The information security incident handling process shall retain complete records for tracking
and review.
(10) Information security emergency response procedures shall include at least one disaster recovery
drill and test each year, and related reports shall be documented and submitted to senior
management.
(11) Establish emergency handling procedures for computer downtime and service interruption.
2. Malicious Software Prevention
(1) Regularly scan computer systems and data storage media for viruses and malicious programs.
(2) Servers and personal computers shall use antivirus software comprehensively and update virus
definitions in a timely manner.
(3) Promptly announce the latest information regarding computer viruses.
(4) Provide ongoing awareness via email: external files or emails with uncertain content shall be
scanned for viruses before being opened or used.
(5) Software licensing requirements: the use of unauthorized software is prohibited; a comprehensive
software inventory shall be conducted once each year.
(6) Conduct email social engineering drills on a regular basis, provide training to personnel who
mistakenly open emails or links, and retain relevant records.
3. Daily Operations Handling
(1) Regularly back up important data and software.
(2) Regularly test backup data to ensure the availability of backup data.
(3) In principle, backup data shall be stored offsite in locations that meet security standards.
(4) Backups of important data shall retain at least three generations (three days of daily
backups).
4. Network Management
(1) Use appropriate network firewall mechanisms to defend information system security.
(2) In principle, regularly test for security vulnerabilities in the network environment, and update
online firewall protection security codes daily through scheduled management.
(3) Announce computer network security matters at any time via email.
(4) Regularly review the implementation of computer network security control items.
5. Handling and Security of Storage Media
(1) Store media in a secure environment in accordance with storage specification requirements.
(2) For transmission of sensitive information, adopt protective measures such as data
encryption.
(3) Sensitive data stored in portable media shall use encryption/decryption or other protective
measures.
(4) Disposal of media containing confidential or sensitive data (hard drives, USB storage devices)
shall be handled by designated personnel or stored in controlled-access areas.
(5) Media disposal may proceed only after data verification in coordination with the department
supervisor and approval by higher-level supervisors, after which physical disposal shall be
performed.
6. Exchange Between Information and Software
(1) Recipients of important system documents must be authorized by the system owner.
(2) Access to important system documents shall be controlled by account and password to grant
appropriate permissions and protect the security of system documents.
(3) For replacement and use of important data documents and software, record in detail the versions,
quantities, and other relevant information.
(4) For electronic data interchange (EDI), apply protective measures such as account/password
control, electronic data encryption, or digital signature authentication based on the security level
of the data.
(5) In processing sensitive data, appropriate strict security mechanisms such as digital signatures,
authentication, and encryption/decryption shall be used.
7. Principles for Using Personal Email
(1) In view of issues that may arise from abuse of email (such as spreading false rumors, forwarding
pornographic images or text, forwarding others’ articles, advertising emails, or leaking business
secrets), the use of personal email shall be regulated and communicated.
(2) Principles for using email (e-mail)
(a) If email use involves spreading false rumors, forwarding pornographic images or text, forwarding
others’ articles, defamatory emails with false content, advertising emails, or suspected leakage of
confidential information, the employee shall bear the related legal responsibilities.
(b) Use of the Company’s email shall comply with administrative ethics, intellectual property
rights, national secret protection regulations, the Personal Data Protection Act, and other relevant
regulations.
(c) After receiving emails, employees shall, in principle, delete such emails from the mail server
immediately to avoid excessive occupation of server space, and only retain communication records and
log files for reference.
(3) Application and cancellation of email accounts
(a) Upon onboarding, employees shall complete the [System/Email Account Application Form]. After the
relevant application is jointly submitted by the unit supervisor and approved through the signing
process, it shall be submitted according to the unit level to the Chairman for approval. The
Computer Center shall then grant the corresponding network permissions based on the application
contents and items.
(b) After an employee resigns, once the information unit cancels network access rights, the email
account shall be deleted accordingly, or retained temporarily for a two-week period and handed over
to the successor.
E. Access Control
1. Access Control Operation and Maintenance Requirements
(1) Establish procedures for opening data access to external entities.
(2) When granting maintenance vendors access for system maintenance or data access, written
documents (e.g., maintenance contracts) shall include the rights and obligations of both parties and
the penalties for breach.
(3) Strictly control access permissions opened to external entities due to business needs (including
upstream and downstream parties, maintenance vendors, outsourced contractors, temporary staff,
etc.), and open access only after risk assessment.
2. User Access Management
(1) Establish control mechanisms for reviewing user access permissions to prevent them from being
known by irrelevant personnel.
(2) Update user change request data at any time and retain relevant documents:
(a) Strictly keep application data for user accounts and passwords.
(b) Regularly check and delete duplicate or idle user accounts.
(c) Establish strict identity verification procedures for forgotten password handling.
(3) Promote to all employees to avoid using personal-related information (e.g., birthday, ID number,
unit abbreviation, phone number) as passwords, and not to borrow or use others’ accounts and
passwords.
(4) Passwords shall be changed according to the prescribed schedule.
(5) Passwords shall be at least six characters (inclusive) or more.
(6) For multi-user information systems, establish user registration management procedures and
records.
3. Network Access Control Measures
(1) Define security levels or classifications based on the security requirements of each application
system.
(2) Establish appropriate access permission management methods based on network types (Internet,
Intranet, Extranet).
(3) In principle, avoid using shared accounts for information systems and network services.
(4) Network services shall establish complete usage authorization procedures.
(5) Adjust firewall management policy settings appropriately based on the environment or business
needs.
(6) Establish logical domain access control mechanisms based on business nature or task assignments
(e.g., Virtual Private Network (VPN)).
(7) For external connections, establish identification methods through checking source user
addresses to determine the origin of connection activities.
(8) Based on risk assessment, manage and control users’ connection functions through firewall
management.
(9) Establish control measures to monitor network routing for the source and destination addresses
of connections.
4. Operating System Access Control Measures
(1) Restrict login operations; disconnect connections when idle for a certain period without
activity.
(2) Keep logs (LOG FILE) for abnormal login procedures, and assign dedicated personnel to review
them regularly.
(3) Users shall have unique identifiers or traceable group identifiers.
(4) After system software installation, immediately change the vendor’s default password.
(5) Each year, review system account permissions and the responsibilities of the account holders by
level, and retain records for reference.
5. Application System Access Control Measures
(1) When evaluating application systems, consider protection mechanisms such as automatic logout
after task completion or after a period of inactivity.
(2) In principle, password files of application systems shall be encrypted using random encryption
rules before being stored.
(3) Shared system programs may be used only after passing strict identity verification
procedures.
(4) Establish authorization procedures and authorization levels for changes to shared system
parameters, and keep change/setting records in electronic or paper form.
(5) For high-risk applications or database systems, strictly restrict connection operation
requirements.
(6) Processing of confidential data must be performed in an independent or dedicated computing
environment.
(7) Properly retain all updated versions of application systems.
6. Monitoring System Access Control Measures
(1) Exception events, abnormal system access, and information security incidents shall be recorded
and handled as necessary.
(2) Record contents should include, where possible, the user ID, computer identification data or
URL, login/logout date and time, and incident descriptions.
(3) Regularly audit account usage and allocation of system access permissions.
(4) In principle, access to sensitive data shall be recorded for reference.
(5) Assign dedicated personnel to manage access and custody of application source code, databases,
and executable files.
7. Mobile/Portable Computer Operations
(1) The information unit shall maintain a register of portable computers used by each unit. Users
are responsible for custody of the physical device, management of software and data security, and
ensuring the correctness and legality of the software they use.
F. System Development and Maintenance
1. System Security Requirements
(1) Server operating system hotfix updates shall be conducted in accordance with proper
authorization procedures, and the suitability of the update shall be thoroughly evaluated and
reviewed to ensure that the corrective action does not compromise the system’s original security
controls.
(2) Prior to major system changes, proactively announce via email the scope, timing, and possible
impacts of the changes.
2. Application System Security
(1) After changes to an application system, the related control measures and procedures shall be
checked to ensure they remain effective.
(2) When planning and analyzing an application system, security requirements shall be included
in the considerations.
(3) Establish update records for application executable code.
(4) Old versions of software and system documents shall be retained during version updates.
(5) Updates to application executable code shall be limited to authorized management personnel
only.
3. Password Control Measures
For highly sensitive data during transmission or storage, encryption technologies shall be
used.
4. System File Security
System file security control methods shall be determined according to actual conditions and handled
using either automatic system controls or manual controls.
5. Security for Developing Information Systems
(1) Outsourced development contracts shall specify copyright ownership and incorporate information
security requirements.
(2) Development, testing, and production operations shall be separated by using different servers or
different databases.
(3) When contracting vendors to develop information systems, performance clauses and related
penalties shall be included.
6. Establish Packaged Software Usage Rules
(1) When modifying packaged software, confirm whether the modification involves vendor copyright
issues.
(2) Regularly evaluate and perform Servic pack updates for packaged software.
(3) For subscription-based packaged software during the contract period, maintenance agreements
shall be signed with distributors and information security requirements shall be incorporated to
support system maintenance and technical support operations.
G. Internal Audit and Others
1. Considerations for Security Policy and Technical Compliance
(1) Relevant measures shall retain records for internal audit purposes.
(2) Regularly review records in the system related to information security (system logs).
(3) Regularly review information security–related log records (such as operation logs and backup
records).
(4) Designate dedicated personnel responsible for managing information security–related log
records.
(5) Use appropriate audit software tools to inspect all software installed on personal
computers.
(6) Establish rules for the storage, processing, and disposal of software usage records and
data.
(7) Implement a system capable of retaining information security–related log records that are
sufficient to serve as evidence for tracing hacker intrusions.
II. Internal Audit Considerations
(1) Establish internal audit management regulations of the Company.
(2) Regularly audit the implementation status of information security matters.
(3) An information security audit plan shall be established (including audit items, scope,
procedures, and personnel) and publicly announced.
(4) Audit personnel shall receive proper training and be assigned tasks in advance.
(5) Audit results shall include background description, audit items, audit process, findings, and
recommendations for improvement.
(6) Audit results shall be documented and retained for record and reference.
III. Regulatory Compliance Requirements
(1) The information unit, legal personnel, or audit personnel shall continuously implement the
collection, disclosure, and execution of matters related to personal data protection regulations,
organizational record retention regulations, and intellectual property protection laws.
(2) Records related to information security shall be retained in accordance with the requirements
stipulated in the Personal Data Protection Act.
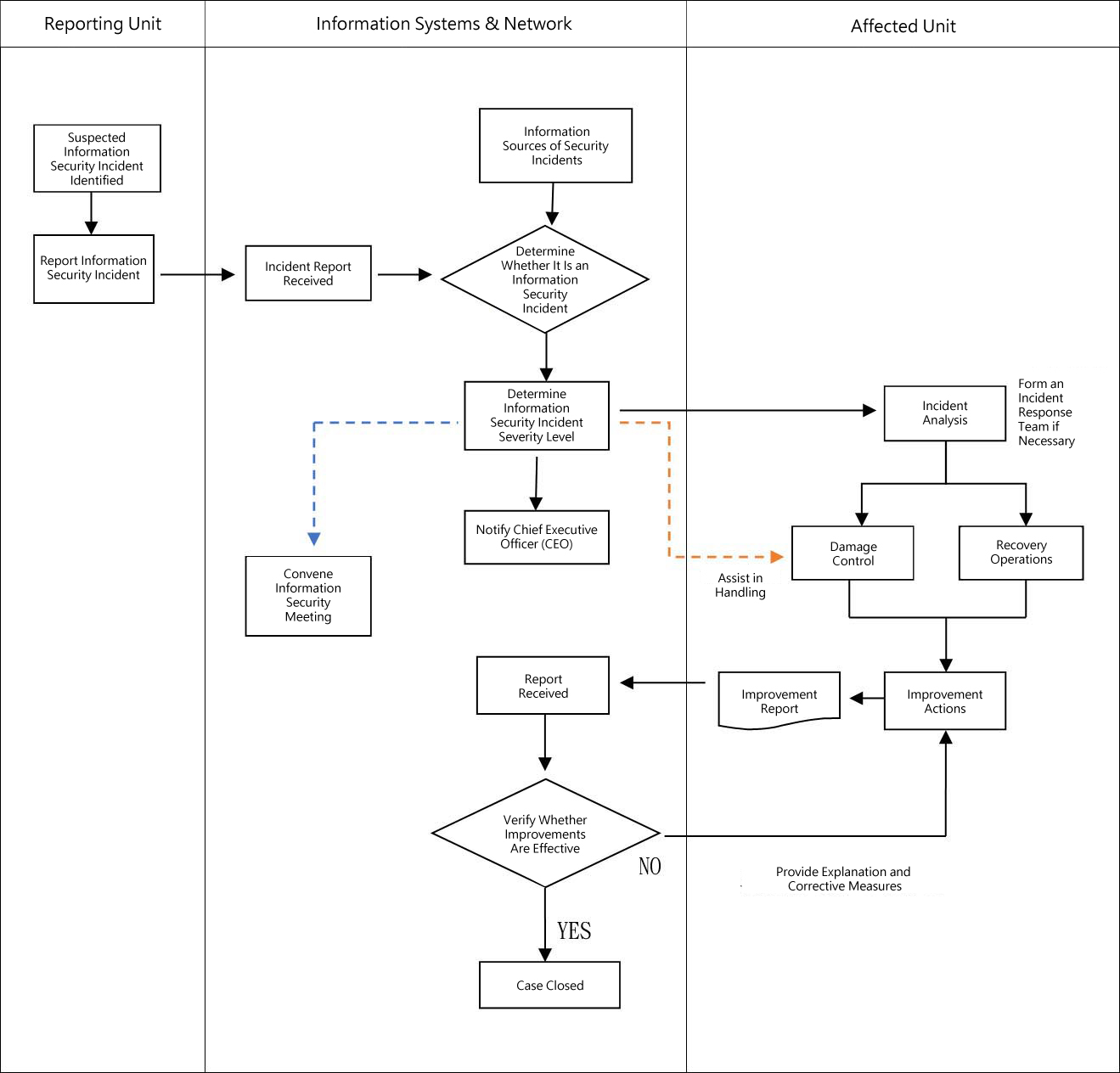
IV. Information Security Incident Reporting and Response Procedures
V. Supplementary Provisions
1. Implementation
This policy shall come into effect upon approval by the Board of Directors. The same shall apply to
any subsequent amendments.
Approved by the Board of Directors on December 19, 2024.
